Quantum communication offers a networking approach that is governed by the laws of quantum mechanics which is more secure and much faster than current digital networks.

Image Credit: Yurchanka Siarhei/Shutterstock.com
Computers across the world are connected by the internet. Current communication methods are vulnerable to being hacked by sufficiently powerful computers. Quantum communication is a secure way of creating a network. Which is much more secure than the methods used today.
Advantages of A Quantum Network
A quantum network can connect quantum devices like quantum computers and quantum sensors over large distances. Current digital networks distribute information in bits that can be either 0 or 1. A quantum network uses quantum bits or qubits that can be 0 and 1 at the same time.
This property of quantum mechanics will allow for a range of novel innovations including a level of privacy, security, and computational power impossible to achieve with today’s methods. For example, quantum computers can solve tasks in minutes that would take years to accomplish on the fastest computer available today.
Building a Quantum Network
A quantum network requires connecting many users together in different cities across the globe. The very properties that make quantum communication secure also make it difficult to implement in a network. When a measurement is carried out on a quantum state, the act of measuring destroys that state while preserving the information. This means data copies cannot be kept. Parts of a data package cannot be read and redirected to another place in a network, like in conventional networks.
One technique proposed is to implement a quantum network with “trusted nodes”. In this method, quantum communication is established between 2 nodes. Then the quantum information is converted to classical data using a transmitter.
The received classical information is stored and then a copy is converted back to quantum signal before being transmitted on to the next node. Here the, “trusted” node is vulnerable to hacks. This method is also complex and resource-hungry as it requires many pairs of receivers and transmitters.
Access networks are a way to improve on the drawbacks of the “trusted nodes,”. Access networks, also known as active switching, work much like a conventional telephone switchboard. Information arrives at one node, which is connected to an onward node and disconnected from the incoming line. The limitations of active switching are that it is slow, doesn’t provide simultaneous access, and only a few connections are possible at a time. It is also not completely secure. Using quantum entanglement for networking has been the most successful approach so far.
Quantum Entanglement
Entanglement is a property of quantum mechanics. A simple description can be followed with the help of figure 1. When a coin is tossed, there are two possible outcomes. Heads or Tails (denoted as H and T in figure 1). Assume two users, Alice and Bob (figure 1), toss their coins independently at two different locations.
The outcome of the coin toss will be completely random for each without any correlation between the two. However, in quantum mechanics, a pair of coins, or quantum states, can be prepared such that they are entangled.
Once entangled, when Alice and Bob toss their coins independently in two different locations they each get the same outcome. When Alice gets a “head” so will Bob, irrespective of the distance between them. This phenomenon is quantum entanglement. Albert Einstein famously called it “Spooky action at a distance.”
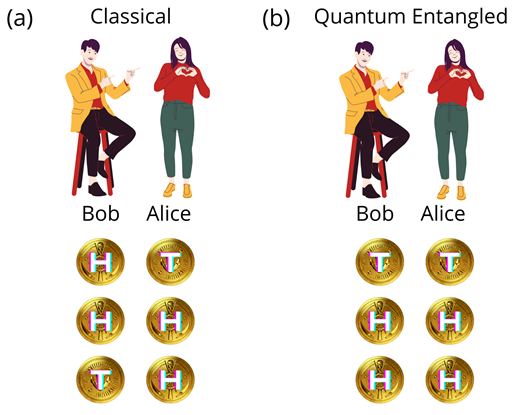
Figure 1: Outcomes of independent coin tosses by Alice and Bob in (a) classical and (b) quantum entangled conditions. H and T denote the head and tail sides of a coin. Image Credit: Ilamaran Sivarajah
To establish quantum communication with entanglement, a secret key is distributed to the users. Quantum Key Distribution (QKD) is a mechanism for agreeing on encryption keys between remote parties. QKD relies on the properties of quantum mechanics to ensure that the key has not been observed or tampered with in transit, thus ensuring that the “coin toss” outcomes for Alice and Bob are the same.
A quantum source is required to create entangled pairs of coins. In reality, the entangled states are created based on different quantum systems. For example, from cold atoms or trapped ions. The entanglement pairs are transported with particles of light called photons. One half of the pair is sent to Bob and the other to Alice.
Quantum Network with Entangled Pairs
To build a network with entangled pairs, first, many entangled pairs have to be created. Then they are distributed to different nodes. In figure 2, entangled pairs are represented by dark and light circles of the same color. The pairs are then distributed such that each user receives one-half of several pairs.
In figure 2, each user receives one-half of three entangled pairs. At least one color pair links a user to one of the other users. This ensures that every user is connected. Each pair creates one network link. When distributed correctly, a fully connected network can be created.
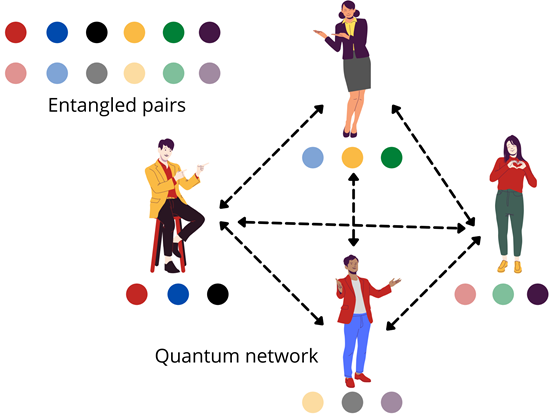
Figure 2: Entangled pairs are denoted by dark and light circles of the same color. One-half of three different entangled pairs are distributed to the users of a quantum network. When distributed correctly at least one color pair links a user to one of the other users. Image Credit: Ilamaran Sivarajah
In a quantum network, the entangled information is distributed by fibers. Traditional large-scale fiber communication infrastructures are adapted for quantum communication. Cryptographic algorithms, called post-quantum cryptography, are developed that are secure against both quantum and classical computers. They can operate with existing communications protocols and networks. Apart from secure communication, digital signatures, anonymous messaging and authentication are some of the tasks accomplished by a quantum network.
British Telecom (BT), a telecommunications company in the United Kingdom, is building the world’s first quantum-secured commercial metro network. This network would operate from London to Bristol.
Future Challenges and Outlook
To build large-scale networks, some core technical challenges have to be overcome, such as designing network stacks and building concepts to extend communication across long distances. A substantial amount of conceptual work is also needed in the development of novel networking protocols and of quantum algorithms.
A fully functioning quantum network would have the capability to transmit large volumes of data across immense distances at a rate very high speeds.
References and Further Reading
A. S. Cacciapuoti, M. Caleffi, F. Tafuri, F. S. Cataliotti, S. Gherardini and G. Bianchi, "Quantum Internet: Networking Challenges in Distributed Quantum Computing," in IEEE Network, vol. 34, no. 1, pp. 137-143, January/February 2020, doi: 10.1109/MNET.001.1900092.
Sasaki. M et al, "Field test of quantum key distribution in the Tokyo QKD Network," Opt. Express 19, 10387-10409 (2011) https://www.osapublishing.org/oe/viewmedia.cfm?uri=oe-19-11-10387&html=true
Gyongyosi, L., Imre, S. Routing space exploration for scalable routing in the quantum Internet. Sci Rep 10, 11874 (2020). https://doi.org/10.1038/s41598-020-68354-y
M Peev et al 2009 New J. Phys. 11 075001 https://doi.org/10.1088/1367-2630/11/7/075001
Disclaimer: The views expressed here are those of the author expressed in their private capacity and do not necessarily represent the views of AZoM.com Limited T/A AZoNetwork the owner and operator of this website. This disclaimer forms part of the Terms and conditions of use of this website.