The quantum computing “arms race” is on. As companies race towards a reliable quantum computer, researchers strive for cyber security and cryptology to foil it.
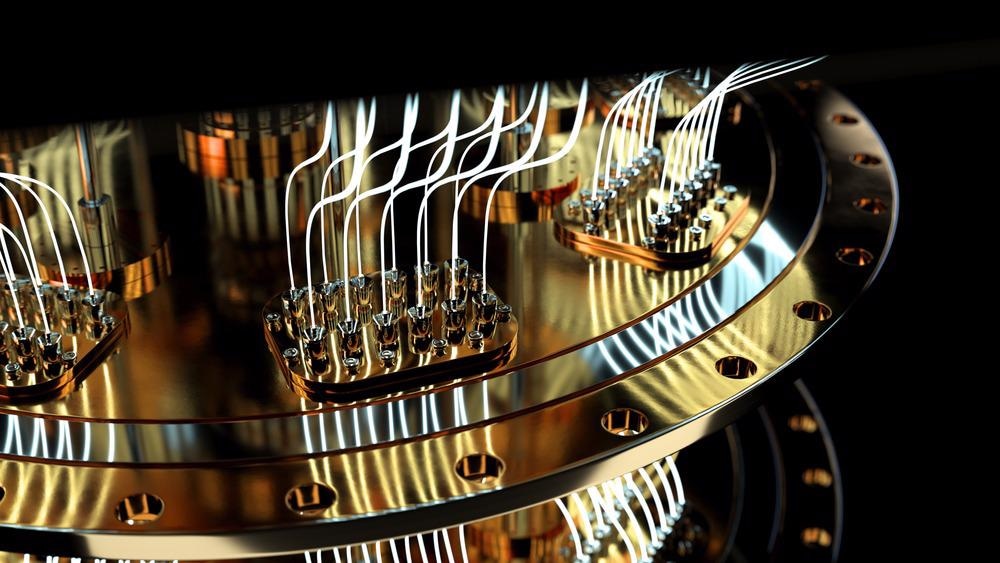
Image Credit: Bartlomiej K. Wroblewski/Shutterstock.com
The race towards quantum supremacy is on, with companies like Google, Microsoft, and IBM all racing towards a viable and reliable quantum computer. Yet, with the promise of the burgeoning computing power of a successful quantum system, comes risk.
Quantum computers with their increased computing power could prove a significant threat to conventional cybersecurity measures.
This means that alongside the race for quantum supremacy, scientists and engineers are also striving to develop cyber-security strategies that are “quantum-resistant.”
Until recently, so-called “brute-force” cyberattacks have required supercomputers or farms of CPUs and, therefore, have not been feasible. However, quantum computers could make such forced infiltrations commonplace, or at best much more straightforward.
Breaking the Code
Currently, messages between two users rely on cryptography to secure them and prevent them from being read by an unauthorized interloper. This is based on a public key, consisting of a very large number widely accessible, and a private key — the product of two very large prime numbers.
These so-called RSA numbers — named for the original designers of the system; Rivest, Shamir, and Adleman — are just waiting to be factored. Fortunately, some of these factored RSA numbers are incredibly large. For example, the largest factored RSA number is 250 digits long and took over 900 years of cumulative computer processing to solve.
IPCC Series: Quantum Technologies: Rethinking Climate Change Solutions
That means, with current computers, it is impossible to factor large numbers efficiently, with the most efficient methods still requiring that a computer try all possibilities. This is akin to a bike thief trying to unlock a combination lock just by trying every single combination of numbers on the dial.
That means that just the sheer amount of time needed to arrive at the correct sequence makes combination locks secure. It is the same with cryptography. Classical computers simply take too long to crack them.
However, the use of an algorithm could be employed to crack the encryption, and quantum computers could be powerful enough to run such an algorithm. Imagine this being like the bike thief breaking out a pair of bolt cutters.
Where Do Quantum Computers Get Their Processing Power?
It is wrong to think of quantum computers as just more powerful classical computers; in reality, they are built on radically different foundations. Classical computers, no matter how powerful, are based on a foundation of bits that can take a value of either “0” or “1”.
Instead of relying on bits, quantum computers are instead based on qubits. Rather than adopting a binary value, qubits can take what is known as a superposition.
A superposition of states is the idea that a quantum system can occupy two or more different states at the same time, even if these states are contradictory.
Video Credit: Centre for Quantum Technologies/Youtube.com
The most famous example of superposition is Schrodinger’s cat, as described in the famous through experiment. This describes a cat placed in a sealed box with a diabolical poison device. The poison is released by particle decay — a quantum process that is completely random.
Treating the box as a quantum system, the cat exists in a superposition of states. Namely, it is both dead and alive at the same time. When the researcher opens the box a phenomenon called “decoherence” occurs and the cat’s state — dead or alive — is resolved.
That means that qubits can both take a range of states or a superposition of these states rather than just 0 or 1. That is how they can crack the massive chain of digits of the encryption in no time at all.
Post Quantum Cryptography: Protecting Against Quantum Computers
The cyber-security industry is currently looking at cryptography methods built on algorithms that quantum computers cannot crack: combination locks that shrug off bolt cutters.
The idea of post-quantum cryptography is for it to be mathematically designed in such a way that quantum computers are no better at breaking this new generation of cryptographic algorithms than classical machines are.
Currently, many symmetric cryptographic algorithms — which use the same cryptographic keys for both the encryption of plaintext and the decryption of ciphertext — and hash functions are considered to be relatively secure against attacks by quantum computers.
As quantum computers become more reliable, they could begin to tackle these algorithms, but the simple act of doubling the key size could then effectively block these attacks again.
This means that protecting against quantum brute force attacks may not require new methods, but simply improvements to existing measures.
Another possible security method against quantum computers could be reliance on quantum key distribution, built on another of quantum physics’ key elements: entanglement.
Quantum Vs Quantum
Once famously described by Einstein as “spooky action at a distance” entanglement involves the creation of two particles or quantum systems that are linked in such a way that a change in one instantaneously causes a change in the other. The “spooky” element of this for Einstein was that this instantaneous change occurs even if the particles are on opposite sides of the Universe.
So, how is this useful for security?
When the quantum system is measured, the values of its elements resolve, just like Schrodinger’s unfortunate cat was resolved as either dead or alive when its box was opened.
Two people send messages using a random quantum-generated key. They share this to encrypt and decrypt messages. The information is sent in an entangled state that resolves when the messengers measure it.
That means that they can tell if someone has snooped on their encrypted message, as anomalies will be introduced when the intruder tries to measure it in order to decrypt the message.
Quantum key distribution is not perfect, though. It cannot be used over a copper ethernet or over Wi-Fi, only via fiber ethernet, LiFi, or laser communications. Also, quantum key distribution will only protect your message as it is transmitted; while it sits on your computer, it is still vulnerable.
Much like classical encryption, quantum key distribution still relies on the use of a cryptographic key, and if this is intercepted messages are still vulnerable.
The development of quantum computers and the side-by-side search for adequate security measures then is almost like the evolutionary “arms race” between predator and prey in the natural world: a quantum arms race built upon increasingly powerful computers, and increasingly robust security measures.
The Feasibility of Parallel Realities According to Physics
References and Further Reading:
Hazara. D., [2020], Shor’s Algorithm: the bane of RSA, Data Driven Investor
Bernstein. D. J., [2010], Grover vs. McEliece.
Disclaimer: The views expressed here are those of the author expressed in their private capacity and do not necessarily represent the views of AZoM.com Limited T/A AZoNetwork the owner and operator of this website. This disclaimer forms part of the Terms and conditions of use of this website.